Surveys and statistics still tell us that one of the most important things a business can do is see what is going on within their business. In the past, a business owner or manager could visually see productivity, equipment misuse, or when they were vandalized. Now we rely on digital devices and clouds to handle so much of how our business is run that it is impossible to rely on hands-on owners or managers to see any issues.
When you did your security research, you were most likely reminded that one device or solution will not solve everything. The main takeaway from those reminders–be leery of the product that says it will. Most businesses, big or small, need layers of solutions to truly protect their assets. The problem that is now arising is that big box companies are selling what they like to call an all-in-one solution. This is a fallacy. One solution is not going to cover all your threats from outside or inside the company. They may offer some version of a lot of different things, but we all know that businesses have focused goals. For many of the larger companies, it is to sell large hardware packages such as a firewall that comes with add-ons.
Okay, so we should all know . . . you need a firewall! But when they tell you to give up your focused URL filtering reports because they have one built-in, think twice before you sign on thinking you are getting the same capabilities. They do not specialize in these included or add-on features. The feature they provide will give you a minimal amount of dry, flat, and unresponsive tools. Yes, you have their firewall and that is a good thing, but question whether you can really use what they provide for the security beyond firewall functionality. Today, security is not just about the firewall.
Things to always check for when reviewing included or add-on solutions:
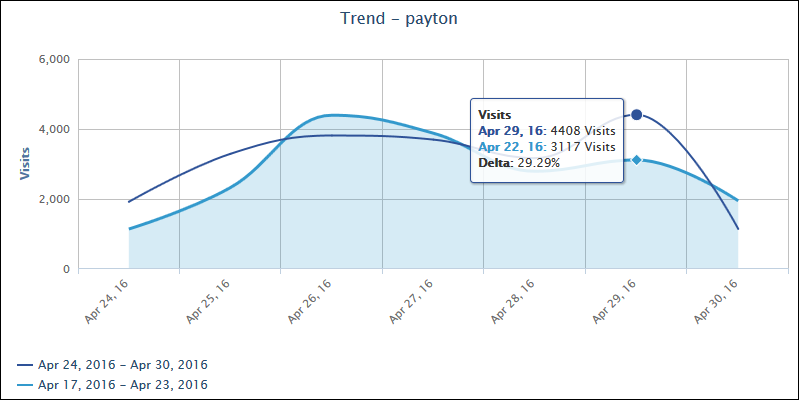
- Drill-down, forensic-level reporting detail.
- Interactive features by user, group, category, etc.
- Manager portal to get managers the information then need without having to schedule time for IT.
- Comprehensive and current URL categories, including designated cloud services.
Do not believe you have to settle for what is included in your all-in-one package. Wavecrest Computing’s advanced employee Web-use monitoring & analytics solution, Cyfin, will provide clear, detailed, and interactive reporting with automatic log file analysis and detection to work with virtually any gateway device and log file format including Palo Alto, Check Point, Forcepoint (Websense), SonicWALL, WatchGuard, and more.
About Wavecrest Computing
Celebrating 20 years in business, Wavecrest Computing, headquartered in historic downtown Melbourne, FL, has provided commercial business and government clients with reliable, accurate Web-use management and Cloud Access Security Broker products since 1996. Managed Service Providers, IT specialists, HR professionals, and business managers trust Wavecrest’s Cyfin and CyBlock products to manage employee Internet usage — managing cloud services, reducing liability risks, improving productivity, saving bandwidth, and controlling costs. Wavecrest has clients worldwide, including General Electric, Lockheed Martin, Florida Department of Health, Siemens, Department of Homeland Security, and a growing list of global enterprises and government agencies. We are a proud long-term GSA contract holder. For more information on the company, products, and partners, visit https://www.wavecrest.net.