![]() Melbourne, FL, Dec. 9, 2013 (GLOBE NEWSWIRE) — Wavecrest Computing, the makers of CyBlock, have just announced the availability of a Cloud version of CyBlock. Now companies have access to the most popular and solid Web Security solution in the Cloud.
Melbourne, FL, Dec. 9, 2013 (GLOBE NEWSWIRE) — Wavecrest Computing, the makers of CyBlock, have just announced the availability of a Cloud version of CyBlock. Now companies have access to the most popular and solid Web Security solution in the Cloud.
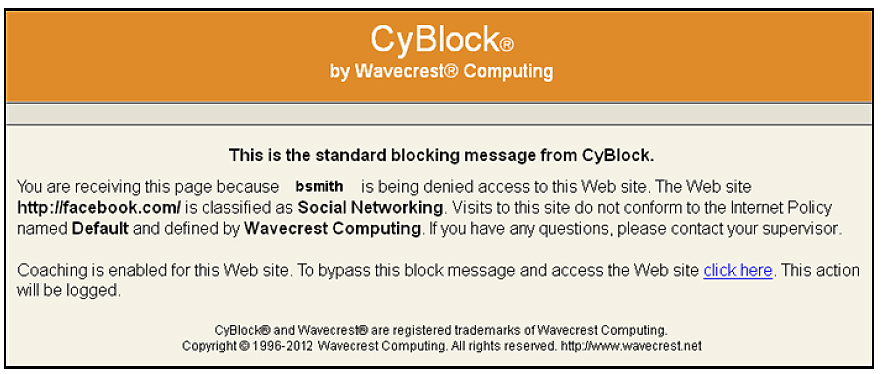
CyBlock Cloud Web Security is an easy-to-implement solution that benefits organizations of all sizes and quickly safeguards your network. Whether you have branch offices, remote users, or just one location, CyBlock Cloud protects your company and its employees allowing you to take advantage of time and money savings. Enforce your company’s AUP by defining one or more Web-use policies to successfully address Internet abuse, legal liability, workforce productivity, and Web security threats.
“We are very excited to be extending our product line into the Cloud market. Now, new and existing customers who are considering a cloud solution have one less worry. Starting today they can access an industry tested and proven solution with a successful 13 year track record. CyBlock Cloud is a perfect addition to Wavecrest’s line of industry leading Web Security Solutions.” CEO – Dennis McCabe
Wavecrest Computing has been the recognized leader in Web-access security and Web-usage forensics solutions for the last 16 years. Our scalable filtering and forensic reporting analysis products are designed to enable organizations to successfully address Internet abuse, legal liability, workforce productivity, and Web security threats. Wavecrest Computing’s client list includes well-known corporations such as Edward Jones, General Electric, Lockheed Martin, Blue Cross Blue Shield, MillerCoors, Rolex, Siemens, and others.
Link to Press Release.