There is so much to be concerned with when running a small business. Economic uncertainty, the cost of health insurance benefits, regulatory burdens, keeping mission-critical operations running–all add up to a stressful experience. Now security concerns include more than just locking the doors; it means everything digital too. And the risks? With ransomware, phishing, insider threats, unsanctioned cloud apps, BYOD . . . lets just say, the Internet usage risks are probably even higher than the front door being left open . . . wide open.
Many small and midsized businesses (SMBs) are without full-time IT departments or even full-time IT personnel, making them a prime target for breaches. But SMBs tend to think they don’t have the resources to handle this type of security, whether it be the financial consideration, personnel needed, or when hardware is preferred, limited space constraints. Since hackers know this, SMBs have to be proactive when it comes to Web-use security–nowadays, even more so than corporations.
The connection between the human and the Internet is a weak link, making it one of the leading access points into a system for a hacker. Whether it’s from the employee clicking a Web link in an e-mail, clicking a malicious ad, or sharing company information with a cloud service, make sure to protect the business by managing that employee-Internet connection. Find a solution that allows you to easily and proactively monitor and secure your employees’ Web activity. Your business is unique–finding a way to solve these issues and concerns will take a unique solution.
A few tips for your Web-use security solution search:
- Find a vendor who will spend the time with you. The cyber world has its own language. It’s important to have a human being on the other end of the phone during the sales process, in customer service, and when you need technical support . . . yup, they still have human beings in technical support . . . go figure! Get with a company who wants to talk to you!
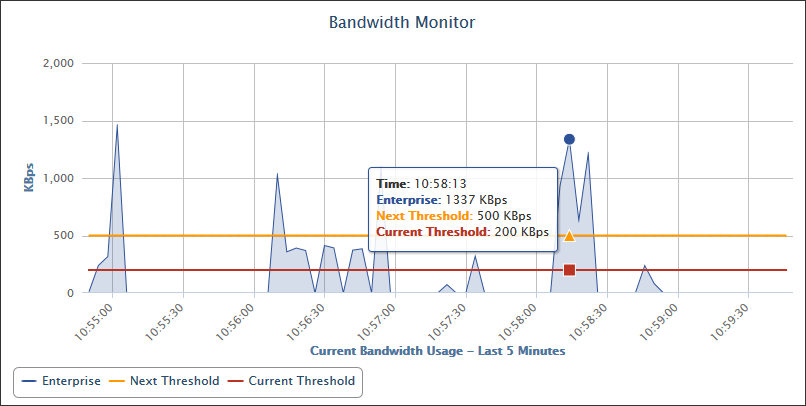
- Of course, it doesn’t help if that vendor doesn’t have what you need so make sure you list the top security priorities for your business. Do you want to filter access to certain Web sites or categories such as social media, or do you want to limit time that an employee may spend on one site? Are you are more concerned with your guest Wi-Fi and BYOD or throttling bandwidth use? Don’t get sold on something that doesn’t meet at least your primary concerns. One solution does not always fit all . . . in today’s cybersecurity world you need to focus on your specific business concerns. Just because an expensive, large scale, all-in-one network security solution or firewall has a Web-use add-on tool does not mean it will give you the pertinent, granular detail and control that you need to protect your mission-critical operations.
- Ask questions. The vendor should understand that you excel at what you do, not what they do. Don’t be intimidated by the security subject. Even those of us in this business spend a lot of time keeping up with the fast pace of cybersecurity. No question is unnecessary. If you think about it, then it is important to you and should be to the vendor too. Refer to Tip #1!
- Last tip for today . . . solutions come in many shapes and sizes. Don’t settle for something that doesn’t fit your business. Your business is special and unique. Your solution should fit and work in your environment without you constantly having to justify it and make it fit in.
Wavecrest can, and wants to, help you!
Wavecrest provides Filtering and User Behavior Reporting solutions that fit your business! Find out more about our Cyfin and CyBlock deployments today. As a customer-centric company, Wavecrest focuses on the needs of each customer. Let us help secure your business with a solution that fits every business size, type, and configuration.
About Wavecrest
Trusted for over 25 years, Wavecrest Computing, headquartered in historic downtown Melbourne, FL, has provided commercial business and government clients with reliable, accurate Web-use management and User Behavior Analytic products since 1996. Managed Service Providers, IT specialists, HR professionals, and business managers trust Wavecrest’s Cyfin and CyBlock products to manage employee Internet usage — managing and reporting on cloud services, reducing liability risks, improving productivity, saving bandwidth, and controlling costs. Wavecrest has commercial and government clients worldwide. For more information on the company, products, and partners, visit https://www.wavecrest.net.




 Keep mission-critical applications running smoothly with
Keep mission-critical applications running smoothly with 