I previously discussed that employee Web use has much to do with human behavior in the workplace, and the management of it is not just an IT issue. All stakeholders and areas of the company can help manage employee Web use effectively. With IT investing time in researching and implementing the most suitable Web filtering and monitoring solution for the organization, collaborators in the company, such as senior managers, HR, and department managers, can get the right information in the right format. Ideally the solution would include a reporting engine or Smart Engine making it possible for collaborators to get a true picture of employee behavior. Here I’ll discuss the features of a Smart Engine and its importance in deriving human behavior from Web-use data.
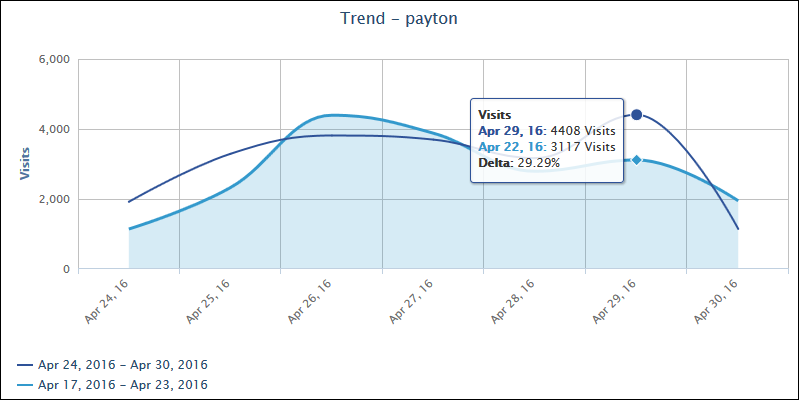
First of all, what is a Smart Engine? A Smart Engine is a powerful reporting engine that helps companies make informed, data-driven decisions and take action on issues concerning the proper use of their network resources. It provides direct, easy, and fast access to data, and low-latency, real-time analytics. With its elaborate, distributed system, it is highly scalable and able to handle petabytes of data. A Smart Engine is built for speed and provides a scalable solution that is optimized for analytics retrieval.
Smart Engine analytics provide the information for reporting–charts and reports–to present accurate and up-to-date Web activity. The Smart Engine utilizes algorithms that perform functions such as determining real Web browsing activity, user names, and time online from Web traffic, and categorizing URLs into logical groups based on content. Without the Smart Engine and its analytics, the reporting components could not provide the adequate information that a company needs to manage employee Web use. The Smart Engine makes technical data usable and manager-ready. Examples of its algorithms are discussed below.
The most important algorithm is one that distinguishes between real Web browsing activity from user clicks (or visits) and background Web activity (unsolicited traffic or hits) by identifying the content of each URL. True visits are actual user clicks that do not include multimedia URLs, such as images, audio Web pages, advertisements, or Web pages that were requested as part of a visit, that is, unsolicited. The differentiation between Web traffic visits and hits is of high importance for companies that want to manage the human factor. Companies can get a true, meaningful picture of the level and type of Web activity occurring in their network.
When Web filtering and reporting products do not include user names in Web traffic records, user Web activity is lost and unaccounted for. The company may not even know that this is occurring. Another algorithm performed by the Smart Engine is a user name caching algorithm that uses the cache user name if available, versus the IP address, allowing you to capture all activity of the user and get more detailed data in reporting.
When users are online, they could be reading a Web page, performing another task in a different application with the browser open, or possibly away from the computer entirely with the browser open. A time online algorithm uses a highly accurate priority method for calculating users’ time online. Managers and IT administrators can quickly see which users, categories, sites, and so on had the most volume of activity and address any potential issues, such as productivity loss, bandwidth slowdowns, and policy noncompliance.
Another algorithm that produces Smart Engine analytics is a categorization algorithm. This algorithm is designed to report on all Web activity. With the extensive content categories available in the Web filtering and monitoring tool, this algorithm categorizes the organization’s Web activity so that managers can analyze their employees’ Web usage. Proper URL categorization detects and identifies a broad range and a high percentage of total Web activity.
The Smart Engine feeds data to the reporting components of a Web monitoring and filtering tool and provides analytics for determining human behavior. You will not get this type of data directly from any firewall on the market today. The raw data itself is only information about machine/network requests. It is not about human activity, but about the machine’s response to a human request to get or push information. The Smart Engine enables companies to quickly create simple Web browsing reports and analyze current or historical Web-use data from human behavior. This human behavior data is what is truly needed to effectively manage employee Web use to keep your employees and network safe.