Because managing employee Web use deals with humans and their actions, it is a continuous process for all sizes and types of businesses, where the goal is to ensure employees use Web access safely for productive, work-related purposes. To attain a high level of success, I believe that this process requires a Web-use management program be put in place that involves many key players in the organization, communication of the company’s Web-use policy, implementation of a reliable tool to monitor and control Web use, and other important activities. In this article, I will discuss the requirements of an effective employee Web-use management program and the activities involved that will bring about safe and productive Internet use by the workforce.
The key ingredient in an effective program is collaboration and communication among the various groups in the company, i.e., senior management, Legal department, IT personnel, HR personnel, department managers and supervisors, and employees. Communication would include IT keeping company stakeholders informed about current hacker threats, as well as HR apprising senior management of pertinent employee Web-use behavior. Collaboration would occur among HR, IT, and department managers in training the workforce. Collaboration would also take place between IT and department heads to select the appropriate Web monitoring and filtering tool.
If you don’t have one already, another necessity of a Web-use management program is to develop a sound Acceptable Use Policy (AUP) consistent with corporate culture. The AUP should describe acceptable and unacceptable Web-use behavior, i.e., company rules for what constitutes desirable, acceptable, unacceptable, and abusive use of the Internet and other network resources. The policy should also clearly state how compliance will be monitored and what the consequences will be to employees abusing the use of network resources. Does your company have an AUP in place that spells out the rules to your employees?
To ensure adherence to the Web-use policy, it should be clearly communicated to the entire workforce, including management, informing them of what is and what is not acceptable in easily understood language. You may also want to have employees acknowledge that they read and understood the policy through a signed acknowledgement. HR and management personnel should hold meetings with workgroups to answer questions and provide any additional information. This fosters open communication in the workplace and allows employees to be more engaged in proper Internet usage.
In addition to communicating the policy to all concerned, another requirement of an effective Web-use management program is training employees on how to use Web access productively and safely. Whether training is conducted or coordinated by HR or in collaboration with managers and other department personnel, training sessions should cover Internet usage and related subjects. Specifically, employees need to be made aware of what sites they are visiting and what they are clicking on the Web. The purpose of training should be to encourage proper, productive, and safe use of network resources while reinforcing the information in the AUP.
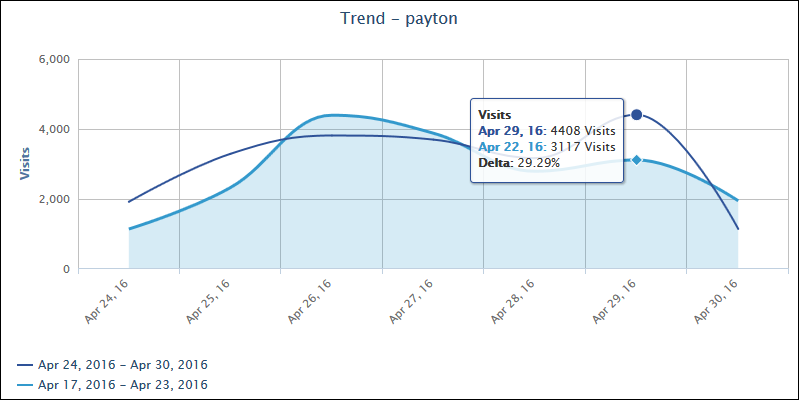
An important requirement of a Web-use management program is to use a reliable software tool that is designed specifically to monitor compliance with Web-use policies and proactively control Web access. The tool should also include a smart reporting engine that distinguishes between user clicks (visits) and unsolicited traffic (hits) and easily presents accurate and up-to-date Web-use data, identifying desirable Web usage as well as unacceptable use and trends. Does your tool include a Smart Engine that analyzes Web traffic to better interpret human behavior? Does it generate easy-to-read, manager-ready reports? Does it give details on employee Web use with drill-down reporting capability? These are key features of a Web monitoring and filtering tool that will benefit IT, HR, and department managers.
Another activity that is necessary is following up with corrective actions when inappropriate Web access is detected. With a policy in place, personnel oriented, the workforce trained, and your Web monitoring and filtering solution actively monitoring and controlling Web use, there are still more activities to do. The tool will inevitably reveal patterns of inappropriate use or disclose signs of outright abuse. These incidents will require attention by HR and management personnel. After identifying the problems, management can take appropriate follow-up actions, such as counseling employees, training or retraining workers, changing work processes, and revising or clarifying the AUP. Managers may also need to institute follow-up audits on individual users and, in worst case, take disciplinary action including termination.
The final element of an effective employee Web-use management program that I will cover involves the establishment of a continuous improvement process by the collaboration team, i.e., HR, IT, department managers, etc. In this process, there would be frequent reviews of employee Web use, new Web services introduced into the network, and new security threats, modifications of work processes, and appropriate revisions of the AUP. All company stakeholders would be involved. What other activities have been effective in your company in managing employee Web use?
Unauthorized Web use can degrade workforce productivity, impact network performance, threaten network security, and create legal liabilities. Any of these outcomes can seriously impact your bottom line. An effective employee Web-use management program is essential to prevent this from happening. If the responsibilities of an effective program are carried out well, misuse and abuse of network resources will be minimized without damaging workforce engagement and morale. Getting accurate, actionable information to all collaborators is a must, and the tool that you are using should be able to provide this information. Next time I will discuss how to get this information with reliable metrics generated by a reporting tool.