This week is the beginning of one of the most popular events of the year… March Madness! An exciting month for sports fans everywhere!
The ex citement during the tournament is addictive! Employees have office pools and discuss the games all through the day. The trouble with March Madness? It occurs during the work day. “An average of 10.7 million people watched March Madness games in 2013, the most since 1994.” During this time, an organization does need to worry.
citement during the tournament is addictive! Employees have office pools and discuss the games all through the day. The trouble with March Madness? It occurs during the work day. “An average of 10.7 million people watched March Madness games in 2013, the most since 1994.” During this time, an organization does need to worry.
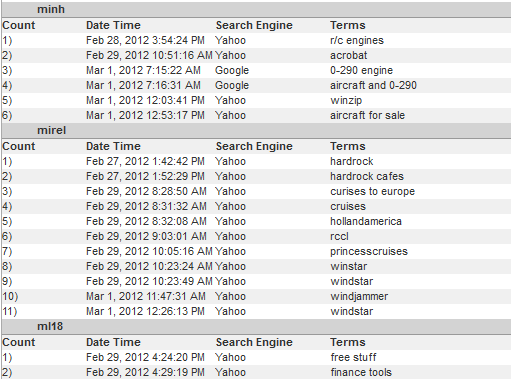
Management needs to be concerned about low productivity, “An MSN poll in 2012 found that 56% of respondents, equivalent to 77.1 million employees, planned to devote at least one hour to March Madness. Using those figures, the damages rise to $1.9 billion for every unproductive hour.” IT, as well as management, needs to worry about the risk of lower bandwidth for critical business operations, “Turner Sports, which operates the NCAA’s website, said 6.8 million unique visitors watched games online during the first week of last year’s tournament. Visitors spent an average of 1 hour and 51 minutes online each time they opened a stream.” These disruptions can cause major problems with the normal operations of any business.
March Madness begins March 18th and runs through the beginning of April. Revisit your organization’s AUP and let your employees know the negative impact their actions could have on the organization.
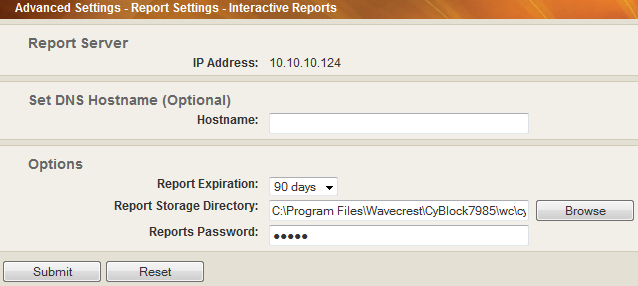
It is a good time to think seriously about making one of Wavecrest Computing’s CyBlock Advanced Web Security solutions a priority. Whether you are thinking you would like to block all access to sports, or thinking you would like to allow some time for your employees to enjoy March Madness while maintaining control over crucial business operations. CyBlock Advanced Web Security solutions can do both. CyBlock can easily block sports or, just as easily, allow for filtering by time frame. Implement flexible filtering by day, hour, or half hour while controlling bandwidth, threat protection, and enforcing your AUP in an easy to manage interface. With deployments options of CyBlock Cloud with the optional CyBlock Mobile Security App, CyBlock Software, CyBlock ISA/TMG, or CyBlock Appliance, Wavecrest can help you find the solution that you need now. Many of these options can be up and running the day you purchase. Do not wait until the Final Four’s final basket!
*Excerpts from Foxbusiness.com, March Madness Ready to Distract Workers Nationwide, By Matthew Rocco Published March 11, 2014