Yes–now is the time. The holidays are right around the corner and definitely require attention now so your business can prepare for the increase in Web usage and the associated risks. There are many reasons for your business to pay close attention to Internet activity at this time of year (and all year). But there is one primary focus that could easily help with all the cyber risks to your business–managing the natural human vulnerability that cyber thieves take advantage of.
Did you know that most breaches are initially caused by employee error? “Ninety-two percent of all incidents are, and 84 percent of all data breaches were, unintentional or inadvertent in nature,” states an article from iapp.org. No matter what kind of data loss or breach it is, human error likely played a very important role.
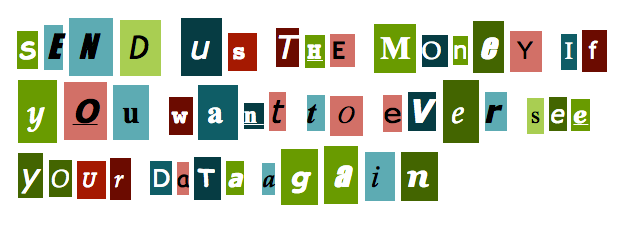
Shopping season can bring out even more human vulnerabilities than usual. Malicious Web sites can look real and carry what looks like legitimate product offerings, advertising can be more enticing with hard-to-resist discounts, and e-mails can come from legitimate e-mail addresses hacked by these talented criminals. Humans’ emotional nature can make it hard to resist when we are all looking for that special or hard-to-get gift. It is important to make sure your business–and your employees–are protected by an easy-to-setup solution that is comprehensive and proactive.
This is easier than you think. Access to a comprehensive Web management solution will allow you to manage usage in a way that suits your unique business philosophy. This includes whether you want to allow or restrict access to certain Web sites at a particular time of day, monitor usage with reporting features by analyzing trends and tracking usage, or just meet compliance and regulation requirements.
This time of year, it is important to spend some extra time paying attention to your organization’s Web use. But Web-use management should be part of your business process and security all year round. Find a solution that is flexible enough to grow or change with you throughout the year, and for this time of year … let them shop … and know you are still being proactive and secure.
Cyfin® provides advanced User Behavior Analytics and Reporting for a wide variety of gateway devices and log file formats. Comprehensive yet easy to use, its customized reporting capabilities supply audience-specific information with reliable metrics, easy-to-read reporting dashboards, manager-ready detailed audit reports, and Smart Engine analytics. Cyfin is available in various deployment options: Cyfin Virtual Appliance and Cyfin Forensic.
CyBlock® Employee Web Filtering and Monitoring Solutions provide advanced Web filtering, threat protection, comprehensive employee reporting, Smart Engine analytics, easy-to-use admin and manager portals, and more. Customers can easily configure CyBlock to monitor and manage compliance with their usage policies. CyBlock is available in various deployment options: CyBlock Virtual Appliance, CyBlock Cloud, and CyBlock Hybrid.
Wavecrest has over 25 years of proven history of providing reliable, accurate Web-use management and Advanced Log File Analyzer products across various industries. IT specialists, business managers, HR professionals, Managed Service Providers, and Forensics Investigators trust Wavecrest’s Cyfin and CyBlock products to easily decipher and manage, and report on, real employee Web activity, manage cloud services, reduce liability risks, improve productivity, save bandwidth, and control costs. Trusted by small, medium, and large government and commercial organizations worldwide. For more information on the company, products, and partners, visit Wavecrest.