Employees are still the central part of all our businesses. Even with all the technology, we still have people to run the operations. The human component of our business is the goal for most hackers. It is easier to find the human weakness than it is to find a network flaw. This human point of infiltration still needs attention, even when you feel your business is secure.
Hackers are smart and agile. It’s a full-time job for them. They don’t get called into meetings, get distracted by co-workers, or have to worry about receiving their W-2 in time for their tax advisors. Their focus is to get into your network using those distractions against your employees. Your employees are busy and focused on what they have to get done, many juggling multiple responsibilities. Hackers like these employees; it’s like candy to them.
Is there any one solution that will remove all risks? No. But there are ways you can help your employees protect themselves and your network. Ransomware, insider threats, phishing–there are so many threats that can halt operations that are critical to your business success. Be aware, prepare.
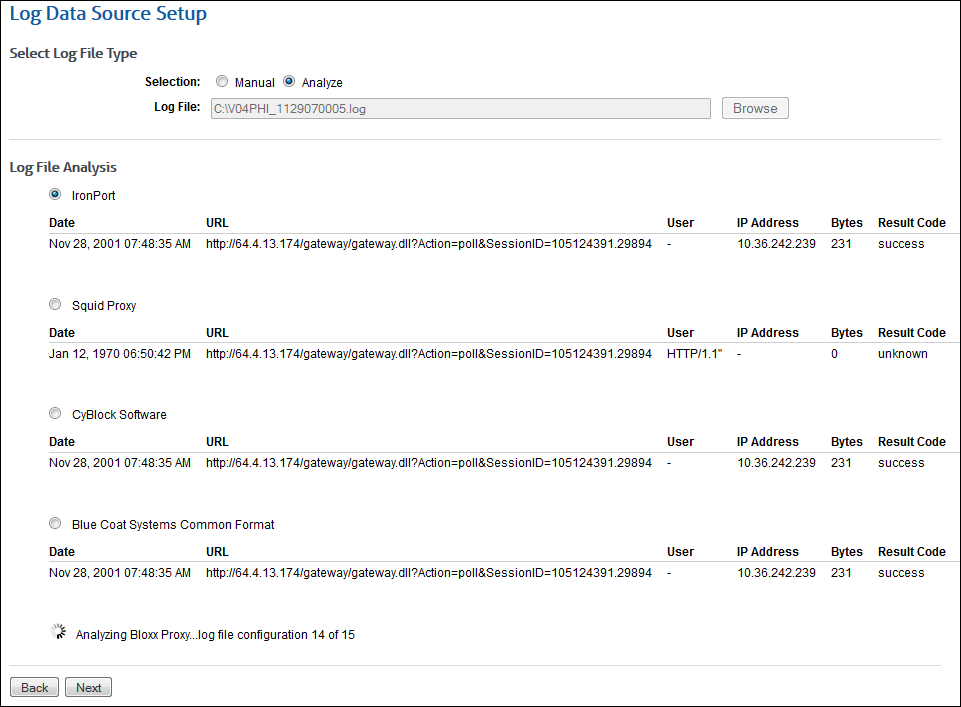
A combination of defenses helps you reduce the risks we all face in business today. Don’t assume one will solve everything. Develop multiple layers of proactive security. This can include anything from making sure your Acceptable Use Policy (AUP) is current or having consistent employee training, to firewall and virus protection, to Web-use comprehensive monitoring and filtering solutions.
It is also important to have a recorded and tested recovery plan in place. Make the assumption that a breach will happen. This way you are prepared. Most importantly, maintain current backups. Make sure that the backups are not accessible through your network!
The “one” solution to protect your business just doesn’t exist. Maintain a combination of defenses and solutions to cover as many risks as possible. Being proactive will pay off in the long run.
Trusted for over 20 years, Wavecrest Computing, headquartered in historic downtown Melbourne, FL, has provided commercial business and government clients with reliable, accurate Web-use management and Cloud Access Security Broker products since 1996. Managed Service Providers, IT specialists, HR professionals, and business managers trust Wavecrest’s Cyfin and CyBlock products to manage employee Internet usage — managing cloud services, reducing liability risks, improving productivity, saving bandwidth, and controlling costs. Wavecrest has clients worldwide, including General Electric, Lockheed Martin, Florida Department of Health, Siemens, Department of Homeland Security, and a growing list of global enterprises and government agencies. We are a proud long-term GSA contract holder. For more information on the company, products, and partners, visit https://www.wavecrest.net.



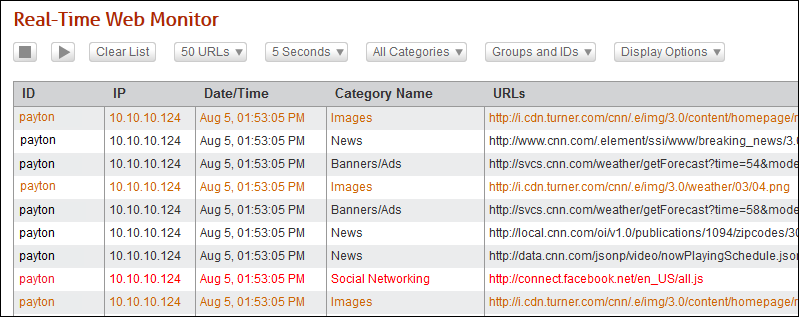
 Get instant real-time information and proactive, reliable control over your network’s Internet users.
Get instant real-time information and proactive, reliable control over your network’s Internet users.