It is important to note that many companies are acquired every day, and this can be a good thing . . . for them. Or maybe not . . . “According to collated research and a recent Harvard Business Review report, the failure rate for mergers and acquisitions (M&A) sits between 70 percent and 90 percent,”Business Review Europe, 2015. More importantly for you as customers, many companies that are acquired leave old customers behind, picking up the pieces of what is left of good service, good prices, good products, and even good friendships.
Service is a critical part of finding the right vendor, especially in security today. There are just too many risks out there that SMBs don’t have the time to fully educate themselves about–they just want to go about their business. So for these SMBs, it is more important to rely on a vendor who they know and trust. When this type of service ends, it can be a major disruption requiring many businesses to decide to deal with the higher prices, more complex contracts, and foreign-based service people with endless ticket systems and long wait times.
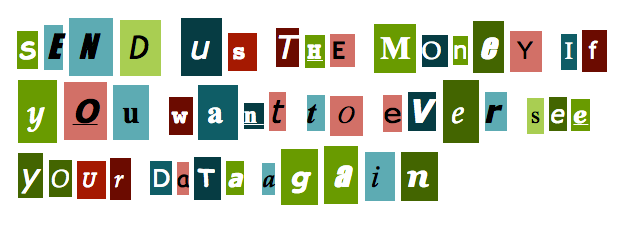
About a year after the vendor is acquired, the new corporation’s policies really kick in, and customers start getting a good idea of changes. Renewal time comes around and instead of your vendor team member calling you to talk about how everything is and if there are any changes to your needs, you get an invoice with extensive terms and conditions that you need to hire a lawyer to understand. Prices increase and you wonder if it is not just to pay for all the terms and conditions being written!
What once was one of your favorite products becomes a burden. Product names change, product lines are cancelled or combined with new product lines, and the confusion builds. Cybersecurity industry acquisitions are becoming hard to follow. One is bought by another, to be bought by another, and then another that has already bought five other companies . . . names mix, divisions are formed, and old relationships are destroyed.
Security for your business should make you feel secure. It should not be something that holds you back or gobbles you up. Don’t be fooled by the promises vendors make just to hold onto you so that they can raise prices at renewal time. You got into business to focus on what you do. It should not be about keeping up with the fine print of enterprise security, the in and outs of the industry acquisitions, confusing contract terms, and high prices. Find that vendor who will become your “stable go-to.” Get a security vendor that makes you and your business feel secure.
About Wavecrest Computing
Celebrating 20 years in business, Wavecrest Computing, headquartered in historic downtown Melbourne, FL, has provided commercial business and government clients with reliable, accurate Web-use management and Cloud Access Security Broker products since 1996. Managed Service Providers, IT specialists, HR professionals, and business managers trust Wavecrest’s Cyfin and CyBlock products to manage employee Internet usage — managing cloud services, reducing liability risks, improving productivity, saving bandwidth, and controlling costs. Wavecrest has clients worldwide, including General Electric, Lockheed Martin, Florida Department of Health, Siemens, Department of Homeland Security, and a growing list of global enterprises and government agencies. We are a proud long-term GSA contract holder. For more information on the company, products, and partners, visit https://www.wavecrest.net.